PCI DSS Compliance Software is often treated as a compliance requirement that teams deal with late in the process, usually around audits or go-live. In reality, it starts much earlier. The way you design your payment flow, choose integrations and structure your backend determines whether your system is easy to secure or difficult to justify under audit.
For developers and tech leads, PCI DSS is less about reading standards and more about making the right architectural decisions from day one.
At Sun*, our teams approach PCI DSS as part of the engineering process, not a separate compliance track. In this article, we break down what the standard actually means for your code, your infrastructure and your deployment workflows.
Key summary
- PCI compliance burden largely depends on three architecture decisions: handling raw card data vs. delegation, tokenizing stored payment methods, and defining your Cardholder Data Environment scope.
- The shift to v4.0 adds focus on payment page script integrity and expanded MFA, but the core principles remain: encrypt data at rest, protect data in transit, control access, log everything, and test often.
- PCI DSS is demanding but achievable for teams that integrate security early in design.
What is PCI DSS?
PCI DSS stands for Payment Card Industry Data Security Standard. It’s a set of security requirements created and enforced by the major card networks like Visa, Mastercard, Amex, Discover through a body called the PCI Security Standards Council.
In plain terms: if your system touches credit or debit card data at any point, you’re required to meet these standards. The goal is to ensure that cardholder data, primarily the 16-digit Primary Account Number (PAN), but also CVV codes, expiry dates, and PIN data, is never accessible to attackers, even if they breach your system.
For developers, PCI DSS translates directly into architecture decisions, coding standards, infrastructure configuration, and deployment policies.
PCI DSS is not merely a compliance task for a dedicated team; the majority of its requirements must be implemented within your code and infrastructure.
PCI DSS v4.0 vs v3.2.1: What Actually Changes for Developers
Compliance helps secure payment information through a “defense-in-depth” strategy. It ensures that if one layer fails, the next layer prevents them from actually stealing usable card data.
The jump from v3.2.1 to v4.0 isn’t a full rewrite but it does introduce requirements that didn’t exist before, particularly around client-side script security and authentication scope.
Here’s a side-by-side breakdown of what changed and what it means for your build.
| Area | V3.2.1 | V4.0 |
| Authentication | MFA required only for remote access | MFA required for all access to the cardholder data environment |
| Web skimming/e-commerce | Not explicitly addressed | Requirement 6.4.3 and 11.6.1 explicitly target client-side script integrity and change detection |
| Password length | Minimum 7 characters | Minimum 12 characters (or platform maximum if less than 12) |
| Vulnerability scans | Quarterly external scans required | Authenticated internal scans added, expanded remediation expectations |
| Customised approach | Compensating controls only | New “customised approach” option for mature security programs to define their own controls that meet the stated objective |
| Targeted risk analysis | Not present | Required for flexible requirements, entities must document their analysis |
When does PCI DSS apply to you?
The short answer: if cardholder data flows through your system or infrastructure in any form, PCI DSS applies. But the scope of what you need to comply with varies significantly depending on your architecture.

Scenario 1. You use a third-party payment processor (Stripe, Adyen, PayPal)
Using a third-party processor reduces, but doesn’t eliminate, your PCI scope. Your risk depends on how card data flows.
If you use hosted payment pages or official SDKs where card data goes directly from the client to the provider, your risk is low because sensitive data never reaches your backend.
However, using custom forms or handling card data in your frontend significantly increases risk. Your role shifts to “secure handling.” You must protect API keys, prevent card data from reaching your servers, and ensure your frontend doesn’t leak sensitive information via logs, storage, or network requests.
Scenario 2. Your server receives and processes card data directly
If your server touches card data, you are fully in PCI scope, and your backend, database, and infrastructure become the Cardholder Data Environment (CDE). This requires implementing strong encryption, network segmentation, strict access controls, and detailed logging. PCI DSS is then a core engineering concern, not just a compliance checklist, impacting every architectural decision for audit readiness.
Scenario 3. You’re dev shop building for a merchant client
Your development role is crucial for PCI DSS compliance, even if you are not the merchant. Insecure code leads to audit failures, regardless of who owns the business.
You must design systems with compliance in mind, document architectural decisions affecting the scope, and align implementation with the client’s validation plan (SAQ or full audit). Developers are part of the compliance chain; your engineering decisions directly impact the client’s risk and ability to operate payment systems safely.
What each of the 12 requirements means in code?
According to Expert Cesar Mora – Compliance & GRC Analyst, when people first look at PCI DSS, it can feel like 300+ individual boxes to check, but if when we zoom out, the standard is actually built around a few big ideas that repeat over and over:
- Document and enforce your security policies and procedures
- Use proper change management for anything that can affect security (firewalls, user credentials, code, configs)
- Apply common-sense security baselines (patching cadence, cryptoperiods, asset inventory, etc.)
- Build strong physical and logical security with MFA, strong encryption, and good key management.
Pair 1. Perimeter and basics
Requirements 1 and 2 are your foundation.
Requirement 1: Install and maintain network security control. This is about network controls – configuring firewalls and VPC rules to restrict traffic to cardholder data systems, with no public access to any database that handles card data.
While requirement 2: apply secure configurations to all system components. It is making sure nothing ships with default settings: remove default credentials, disable unused services and ports, and harden your OS configuration before deployment. No “admin/admin” anywhere in your payment stack.
Req 1 filters what can reach your environment. Req 2 removes the easy ways in once something gets there. Together, they form Milestone 1 of your PCI journey: build a defensible perimeter and remove obvious weaknesses.
Pair 2. Data protection
Requirement 3: Protect stored account data covers what you store and more importantly, what you’re prohibited from storing. CVV must be discarded immediately after authorisation, no exceptions, even encrypted. If you store the PAN at all, it must be encrypted with AES-256 or replaced with a token so the raw card number never sits in your database in usable form.
Requirement 4: Protect cardholder data with strong cryptography during transmission, covering data in motion: TLS 1.2+ on every path card data travels, no TLS 1.0 or 1.1, certificate pinning in mobile apps, and card data must never appear in URLs, GET parameters or application logs.
Req 3 locks down the where of card data. Req 4 protects the journey it takes between systems. The pattern is clear: store less, protect what you must store, and encrypt everything that moves.
Pair 3. Secure Systems
Requirement 5: Protect all systems from Malware and regularly update anti-malware software requires malware scanning across all systems in your CDE. This includes your CI/CD pipeline and build servers, not just production infrastructure.
Requirement 6 focuses on the developer’s role in maintaining secure systems and software by mandating a secure SDLC. Key practices include code reviews, dependency scanning, addressing OWASP Top 10, robust input validation, using parameterized queries, and removing hard-coded secrets. Version 4.0 also adds specific requirements for payment page script integrity.
Req 5 handles commodity threats (malware). Req 6 tackles structural weaknesses in your systems and custom code. Together they’re your “secure systems” milestone: keep software healthy and design security in, not bolted on.
Pair 4. Access control
Requirement 7: restrict access to cardholder data by business need-to-know is about limiting who and what can reach cardholder data. Role-based access control, principle of least privilege applied to IAM policies and database permissions, only the services and users that operationally need card data should be able to access it.
Requirement 8: Identify users and authenticate access to system components covers how that access is authenticated: MFA for all admin access to the CDE, a minimum 12-character password policy and no shared credentials. Every user and service account needs a unique identity.
Req 7 is about authorization (should you get in?). Req 8 is about authentication (are you really you?). Together, they create a clean access-control story: only the right people, with the right level of access, proven with strong identity.
Pair 5. Visibility and Facilities
Requirement 9: Restrict physical access to cardholder data deals with physical access to systems, primarily a data centre concern. For cloud deployments, verify that your provider’s physical security certifications cover this requirement and document that you’ve done so.
Requirement 10 mandates logging and monitoring all system and cardholder data access. Infrastructure efforts focus on audit logging for all card data operations, centralized log management, and retaining logs for 12 months (3 months immediately accessible). Crucially, never log card numbers or CVVs, a common payment logging error.
Req 9 protects the room and the hardware. Req 10 protects the story of what happened. Together they give you traceability: if something goes wrong, you can see who, what, where, and when—physically and logically.
Pair 6. Assurance and governance
Requirement 11: Test security of systems and networks regularly requires regular security testing, quarterly vulnerability scans and annual penetration testing of your CDE. Your application will be tested against the OWASP Top 10, so have a documented remediation process and severity-based SLAs in place before your first assessment.
Requirement 12: Support information security with organizational policies and programs is the governance layer: documented security policies, a maintained incident response plan, and developer security training. Engineers should know the breach response playbook, not just that one exists, specifically what to do and who to notify if card data is suspected to be compromised.
Req 11 is about proving your controls work. Req 12 is about governing them across people, processes, and partners. This final pair turns PCI from a project into an ongoing program.
What changed in PCI DSS v4.0 that directly affects your code
PCI DSS v4.0 released March 2022, v3.2.1 retired March 2024, all v4.0 requirements fully mandatory March 2025. If your system was built to v3.2.1, you will need to implement specific additions to meet the new v4.0 requirements.
Under v3.2.1, many teams focused on implementing specific controls. With v4.0, it’s no longer enough to have those controls, you need to prove they are effective, adaptable, and consistently enforced through your system.
One of the most immediate impacts is the formalization of secure development practices. What used to be implied is now explicit: your SDLC must include code reviews, dependency management, and protection against common vulnerabilities like those in the OWASP Top 10. This pushes security earlier into the development lifecycle and makes it part of everyday engineering work, not a final checkpoint.
Authentication requirements have also tightened, with multi-factor authentication becoming mandatory for all access to cardholder environments. For developers, this means building MFA not just for customer-facing features, but for internal tools, admin panels, and operational access paths.
Logging and monitoring expectations have evolved as well. Systems are now expected to support detection of suspicious behavior, not just record activity for audits. That requires more structured logging, better signal design, and tighter integration with monitoring pipelines.
v4.0 forces a mindset shift: security is no longer something you configure around your system, it’s something your code must actively support, enforce, and make observable.
How tokenization architecture dramatically reduces your compliance scope
Tokenization reduces PCI scope by ensuring your system never handles real card data. Instead of storing or processing card numbers, your app exchanges them for tokens generated by a payment provider. These tokens can be used for transactions but have no standalone value if exposed.
In practice, card data is sent directly from the client to the provider via SDKs or hosted fields, while your backend only works with tokens. This removes the need to store, encrypt, or secure sensitive data, significantly lowering both engineering complexity and audit scope.
However, this approach doesn’t apply to all systems. If you’re building eWallets or handling payments directly, card data may still pass through your infrastructure and full PCI requirements apply again.
5 PCI DSS failures that happen to good development teams
Most PCI DSS failures in development teams aren’t the result of ignoring security. They’re the result of reasonable engineering decisions: verbose logging for debugging, storing data for convenience, using a trusted third-party processor that turn into compliance gaps because the implications weren’t visible at the time.
We found 05 that come up most often and what to do about them.
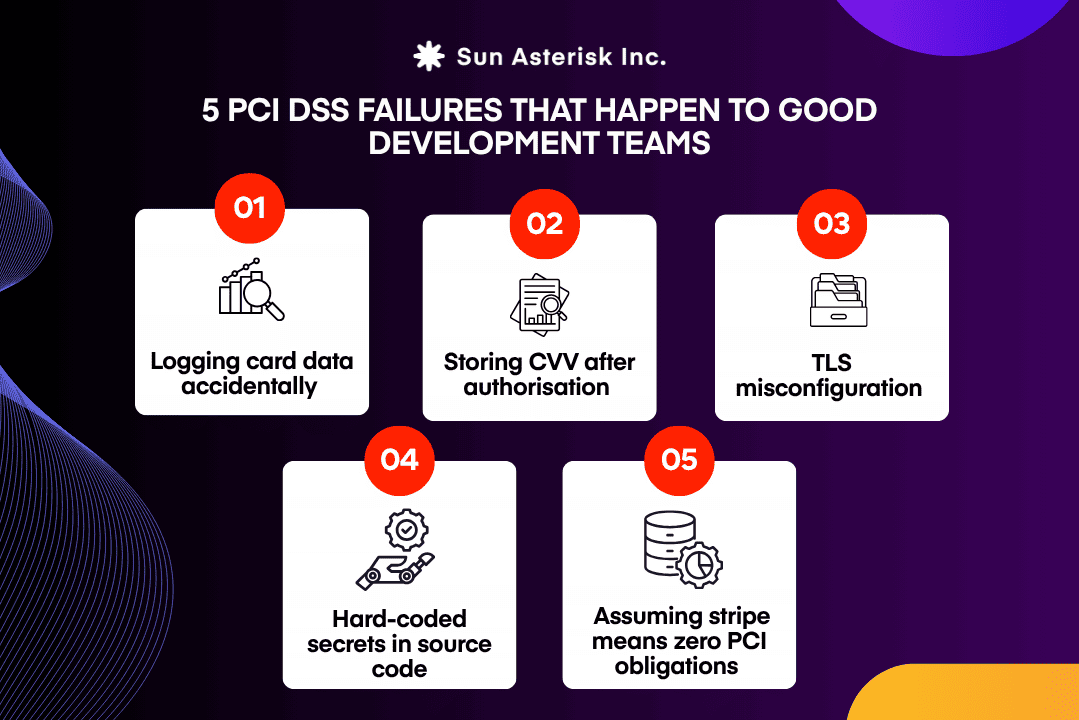
1. Logging card data accidentally
When application logging middleware captures full request and response bodies, even routine troubleshooting can create major security gaps. If a developer enables verbose logging to debug an issue, sensitive data like card numbers and CVVs may end up as plaintext in log aggregators.
These systems often have much broader access than the Cardholder Data Environment (CDE), making the lack of PCI DSS compliance software or automated scrubbing a critical risk.
The issue is that payment endpoints are frequently treated the same as standard routes in middleware configurations. To fix this, you must build an explicit distinction: implement mandatory log scrubbing to mask PANs and strip CVV fields before storage.
Always audit your logging pipeline with card-shaped test data to ensure your PCI DSS compliance software strategies are working. Never allow raw payment payloads to reach your logs without first passing through a dedicated scrubbing layer.
2. Storing CVV after authorisation
PCI DSS Requirement 3.3 strictly prohibits storing CVV data after authorization, even in an encrypted state. Its only purpose is to verify card presence during the initial transaction; once that process is complete, the data must be discarded. Retaining it violates security standards, as no legitimate business case exists for its storage. Integrating automated PCI DSS compliance software can help detect and prevent such data retention across your infrastructure.
This security gap typically occurs in overlooked areas where data lingers like queue messages containing full payloads, improperly scoped cache entries, or audit tables logging raw inputs before validation. To close this loop, you must audit every data model, queue, and log entry in your payment flow.
While developers occasionally mention recurring billing as a justification for retention, this is correctly handled through processor tokenization. Relying on robust PCI DSS compliance software ensures these sensitive values are never self-stored, maintaining a secure and compliant environment.
3. TLS misconfiguration
Although prohibited since 2018, legacy protocols like TLS 1.0 and 1.1 often persist in internal services and mobile apps due to configuration oversight. These outdated standards, combined with weak cipher suites or missing certificate validation in mobile clients, create vulnerabilities that are easily missed without specialized PCI DSS compliance software. Such gaps expose cardholder data during transmission, presenting a risk that far exceeds a simple audit failure.
To resolve this, gain visibility by scanning public endpoints and auditing internal service-to-service communication within the CDE. You must also inspect mobile HTTP client configurations, specifically minimum TLS versions and certificate pinning—while enforcing TLS 1.2 or higher at the load balancer level to reject downgrade attacks.
Utilizing PCI DSS compliance software to continuously monitor these settings ensures your infrastructure remains resilient. Ultimately, audited systems are secured, while unmonitored ones remain a liability.
4. Hard-coded secrets in source code
Hardcoding API keys, encryption keys, and payment credentials into version control is a pervasive security failure, often triggered when developers temporarily hardcode values for local testing and accidentally commit them.
Once committed, these secrets remain in the repository history, accessible to anyone with read access or even the public if the repo is exposed. Without specialized PCI DSS compliance software or automated scanning, these leaks can remain undetected for years, creating an immediate compliance violation.
The solution is structural rather than behavioral. You should leverage secrets management tools, such as HashiCorp Vault, AWS Secrets Manager, or GCP Secret Manager—to remove sensitive data from code and environment files entirely. Integrating PCI DSS compliance software with pre-commit hooks and CI/CD pipelines allows you to scan for leaks before they reach the server.
Any secret ever committed to source control must be treated as compromised and rotated immediately as a high-priority security incident.
5. Assuming stripe means zero PCI obligations
Using third-party payment processors significantly reduces PCI DSS scope because card data bypasses your servers. However, it’s a major misconception that using a processor eliminates all compliance obligations; scope reduction is not scope elimination.
Protecting your Stripe API keys is crucial; their compromise bypasses Stripe’s PCI compliance, causing financial and reputational damage. Correctly using Stripe Elements or hosted fields is also mandatory. Custom card input handling raw data before Stripe’s JavaScript library puts you in scope. You must understand your remaining PCI scope (determined by your SAQ type), rather than assuming it’s zero, to ensure compliance.
At Sun*, our engineering team integrates PCI compliance into Digital Transformation using a Security-by-Design approach with tokenization. We ensure continuous compliance with Automated Compliance checks in CI/CD pipelines and ensure all systems are audit-ready for the highest payment security. If you’re developing payment features and need an engineering partner who understands both the compliance requirements and the implementation.
Let’s talk about your architecture.






